Avoid the Punch of Ransomware
Feb 23, 2016
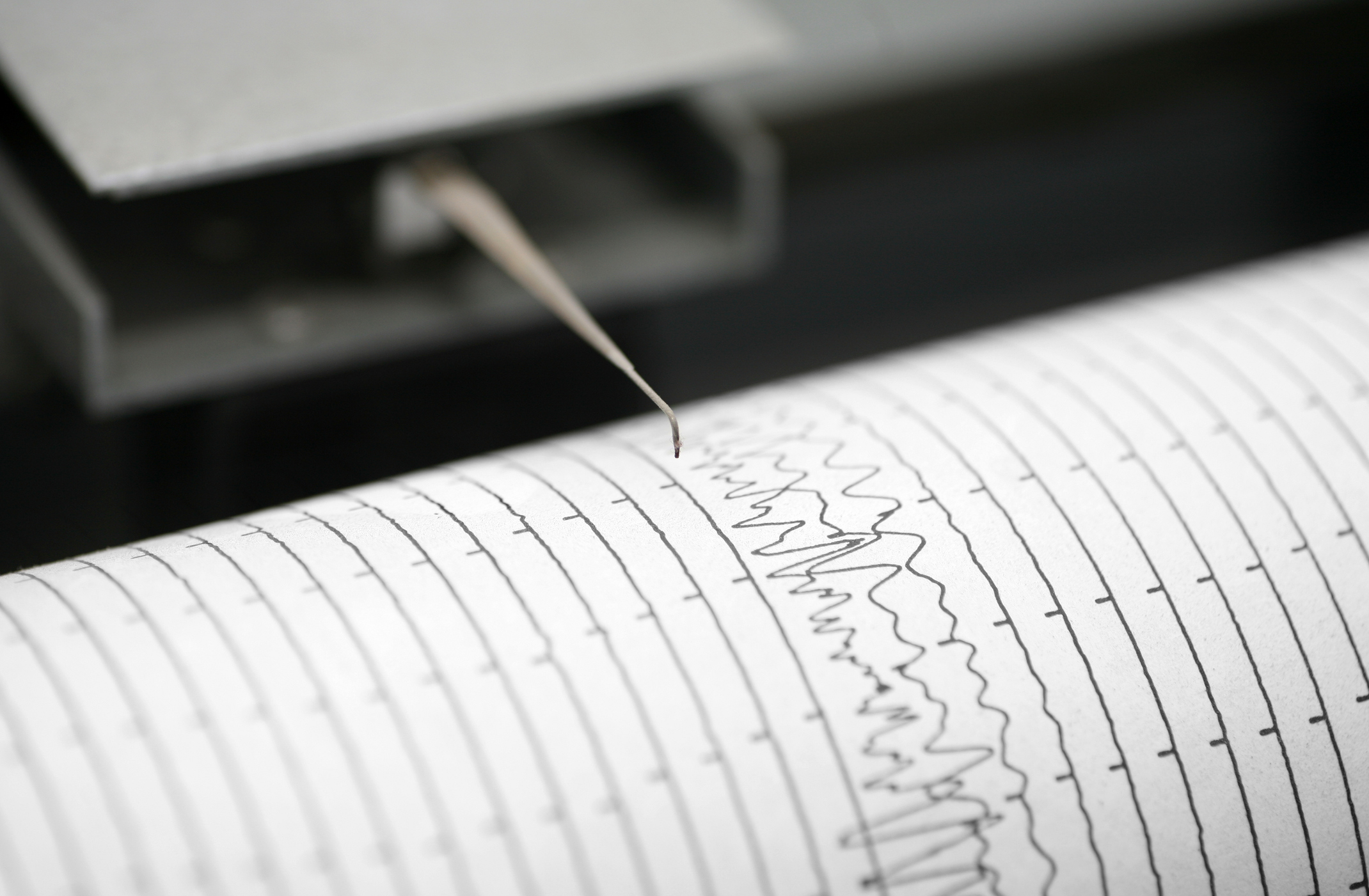
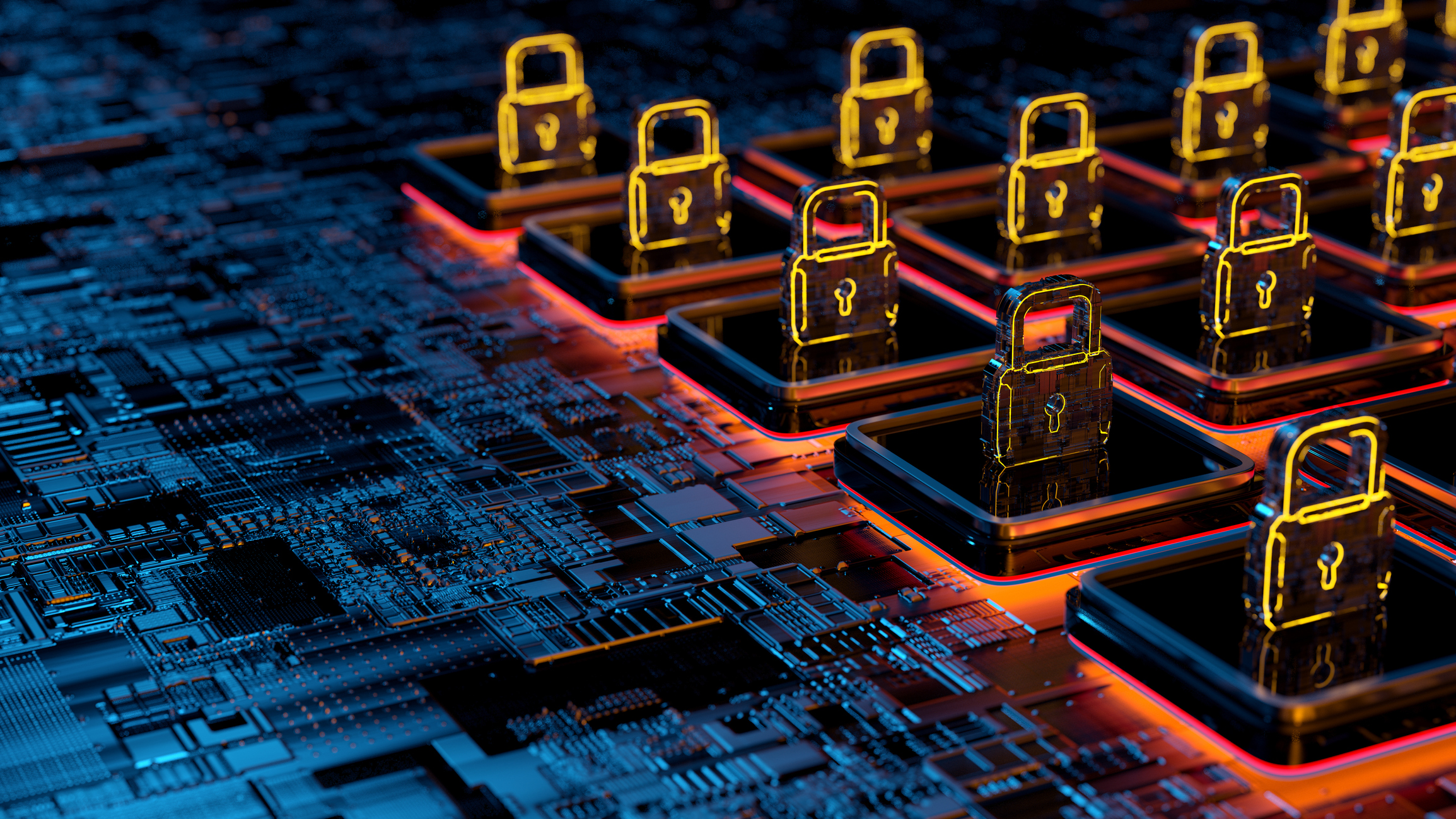
One thing that computers and programmers typically do very well is encryption – so well that it is almost impossible to break. But what if the bad guys use this defensive move for extortion?
If someone in your organization clicks on the wrong link in an email, then they may find out that the result is infection by ransomware. Ransomware infects a computer and encrypts files on the computer and network. Once these files are encrypted, the only way to open them again is with a key that only the bad guys possess. The perpetrators will “sell” you the key to decrypt the files. However, keep in mind that cybercriminals are behind these schemes, so even paying for the key may not get you off of the ropes and guarantee the unlocking or retrieval of your files. Therefore, the questions to prepare your one-two punch become:
- How do you avoid becoming a victim of a ransomware attack?
- If successfully attacked, how can you recover?
We’ve all heard the saying that “prevention is worth a thousand Bitcoins,” right? In the case of ransomware, preventative controls are paramount. So what practical steps can you as a business owner take to protect your digital assets and your company from an attack? Consider this list of proactive ways to fortify your defenses.
- Implement training. In order to protect against an attack, both identification of the risk and education about prevention are vital. Ransomware is often spread by malicious HTML links found inside emails. Therefore, educating your team regarding the different scenarios used to distribute those links is the first line of defense. For instance, “phishing” is a common technique to trick people into thinking that the email is coming from a legitimate source. The email reader thinks the email link will take them to a safe website to track a package or see an order status. Instead, the link releases malicious code to spread the ransomware.
- Educate your team to be extremely cautious of opening any email attachment. Through scenario-based training and social engineering exercises, you can coach your users to recognize “phishing,” “spearing,” “whaling,” or other common attacks. Emphasize not opening attachments from unknown or unverified sources – as well as those that they did not specifically ask to be sent.
- Install security patches and keep anti-virus updated. Many times, the malware containing the ransomware can be thwarted by having the latest security patches and anti-virus software updates. Rather than delay or ignore the prompts to update and maintain patches and anti-virus, install them immediately.
- Have clear policies in place. Be sure your company has clear policies in place to protect your data from ransomware. Clear direction regarding email attachments and file downloads (and the users’ responsibilities) is essential in combating ransomware.
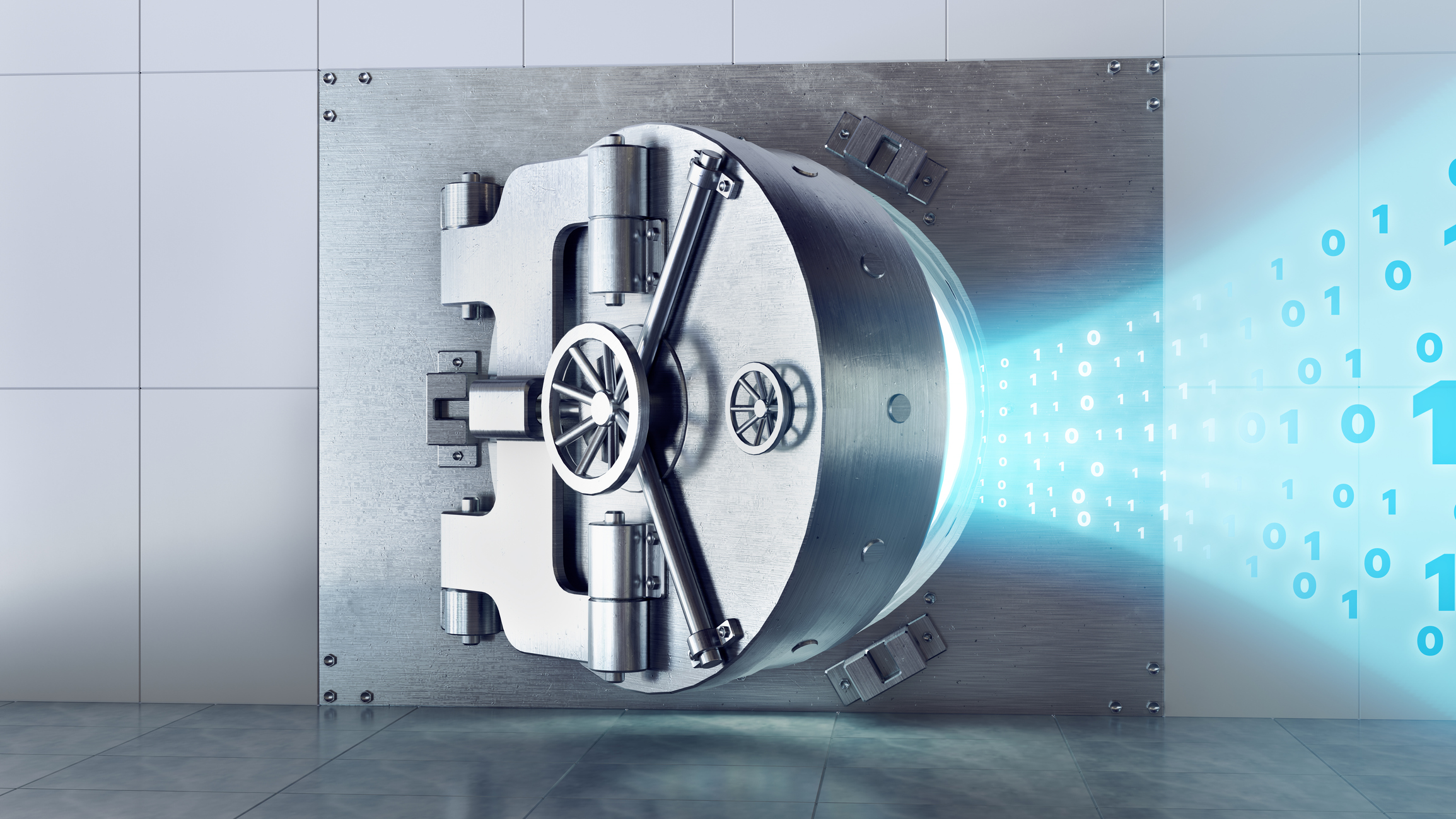
Win the Belt: Create the Ability to Recover Files Prior to the Ransomware
All three items listed above are excellent ways to reduce your risk related to ransomware and protect your data. However, nothing will keep you 100% safe, so you need a plan that will help you roll with the punches if the worst-case scenario occurs. If you are attacked, then your organization needs to be able to recover its files from a version that is not infected. So, back up your data regularly. The appropriate interval is a company-by-company decision, and understanding your data is essential. Consider answers to questions such as:
- How often is the critical data created?
- How often is the company willing to recreate the data that might be lost in an attack?
The prize-winning key is to have a backup solution that will allow recovery back to files from a specific date so that you can recover files prior to the ransomware attack. So beat those cyber criminals to the punch by contacting CRI’s cybersecurity team today and asking for help protecting your organization and its data.