Protecting Your Company Against Executive Impersonation Fraud
Sep 8, 2022
Every year, businesses lose vast sums to fraudsters who compromise legitimate business email accounts to conduct unauthorized transfers of funds. These scams are known as business email compromise (BEC). The FBI received 19,954 complaints about BECs in 2020, and they cost businesses an eye-popping $2.4 billion.
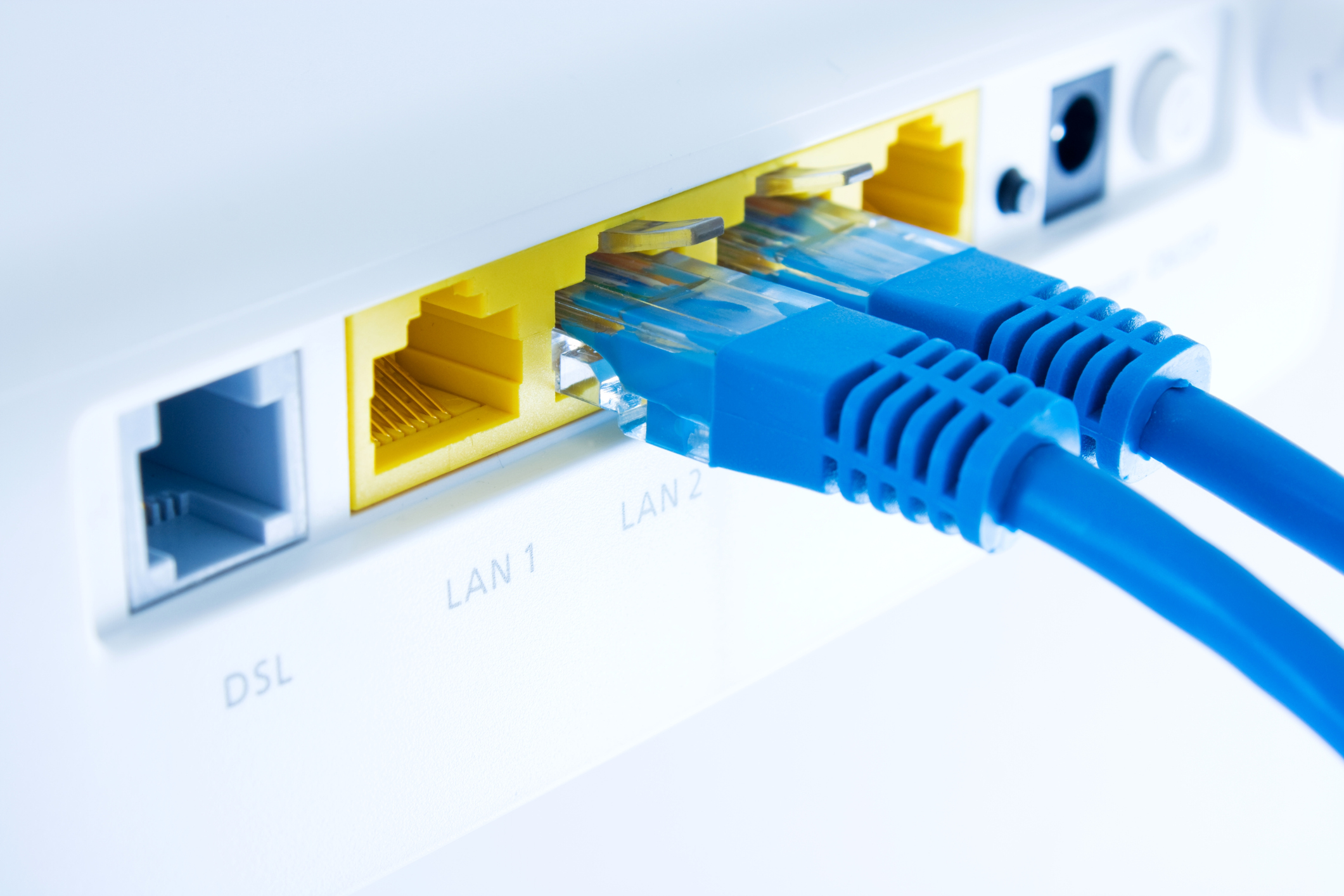
One form of BEC is known as executive impersonation fraud, which entails a skilled criminal (or group of criminals) crafting an email that appears to be from one of the company’s key executives. The domain of the email address may be identical to the company’s domain except for one or two letters (e.g., joe@victimco.com vs. joe@vicitmco.com), or the email address might even be “spoofed” so that it appears legitimate until the recipient hovers the cursor over the address (which reveals the real sender).
The criminals do their homework to make their scheme convincing. They typically scour the company’s website and social media accounts to carefully investigate the executive they are impersonating. Additionally, they research their intended target, who will ideally be someone with the authority to initiate or approve wire transfers.
Spotting Potential Threats
In a world where even an email from you or another executive could be corrupt, it can feel like threats are everywhere. To defend against executive impersonation fraud, it is critical that employees recognize the following warning signs:
- The email appears to be from a senior executive but comes from an address that differs from the official, company-issued domain.
- The sender conveys urgency or secrecy by asking to communicate only through email (perhaps due to supposed regulatory restrictions).
- Payments are directed to foreign bank accounts, especially where the company has never done business.
- The request occurs when the key executive is traveling or unavailable.
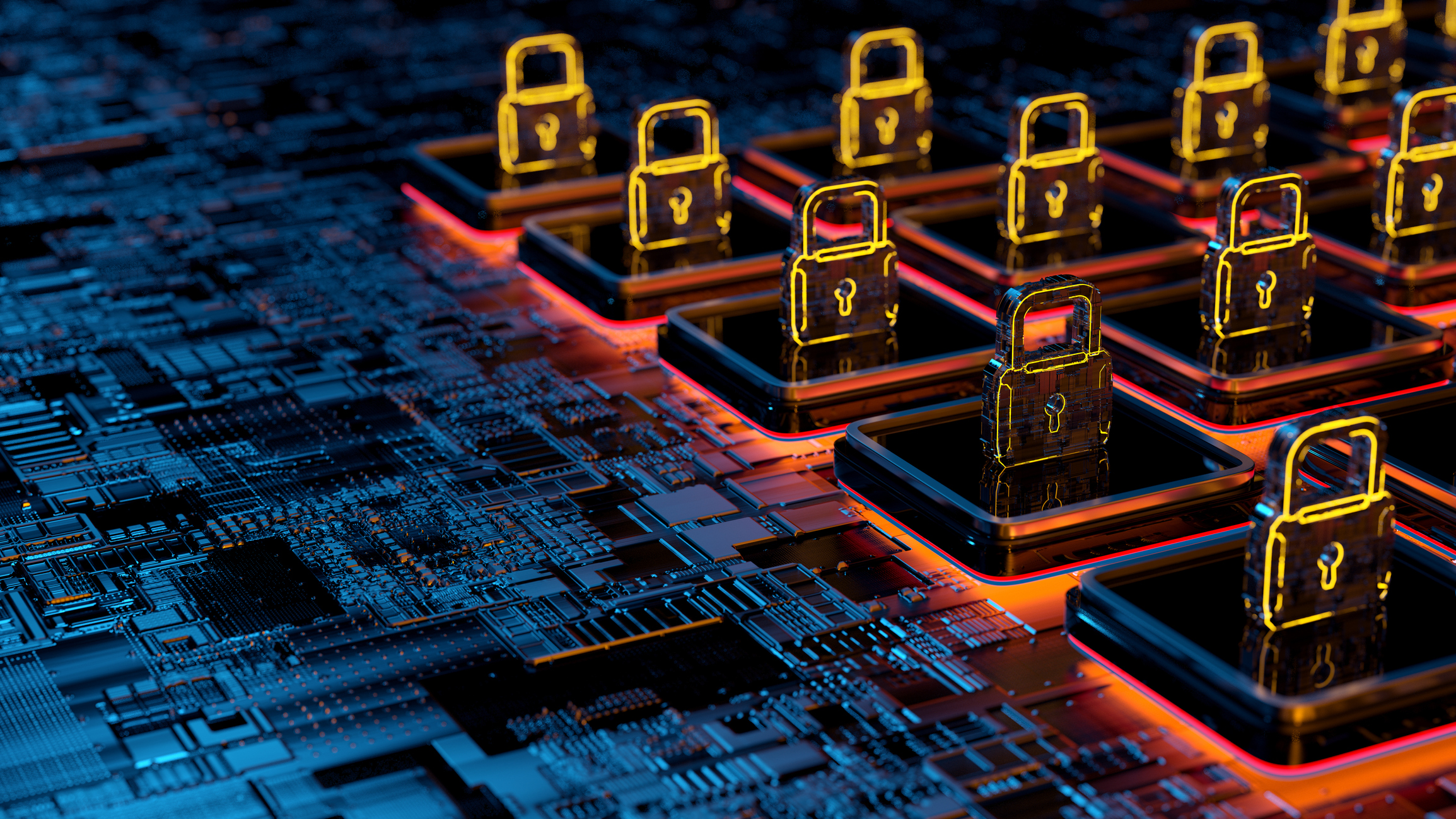
Creating a Defense Against Cybercriminals
Executive impersonation fraud relies on employees’ willingness to bypass normal financial controls. Companies can dramatically reduce their risks with the following basic precautions.
- Create a culture of skepticism. Employees should know that questioning authority — especially in regard to initiating financial transactions — is not only allowed, but strongly encouraged.
- Build employee awareness of the latest email scams. In addition to companywide cybersecurity education, all employees who have authority to request, approve, or execute wire transfers should receive regular (ideally, quarterly) training on common social engineering attacks.
- Implement and enforce a social media policy. Employees should be careful about what they share on social networking sites, especially details about key executives’ travel itineraries.
- Strengthen controls around wire transfers. First, restrict authority for initiating or approving financial transactions to a few individuals. Then, design and implement procedures to verify the origin of all wire transfer requests. Many companies require verbal confirmation from someone calling from a company-issued phone number, followed by secondary verification from another individual via another phone call using an authorization code.
- Document all of these steps. In the event that a security breach occurs, your documentation will be invaluable for showing regulators and prosecutors that your company implemented reasonable and appropriate safeguards to mitigate data loss.
Let CRI Be Your Cybersecurity Defense Ally
Defending against executive impersonation fraud requires you to objectively assess your organization’s threats, vulnerabilities, and internal controls. Please contact a CRI cybersecurity professional for more insights on protecting your company from cyber fraud.