Social Engineering Attacks: Considerations for SMBs
Sep 22, 2020
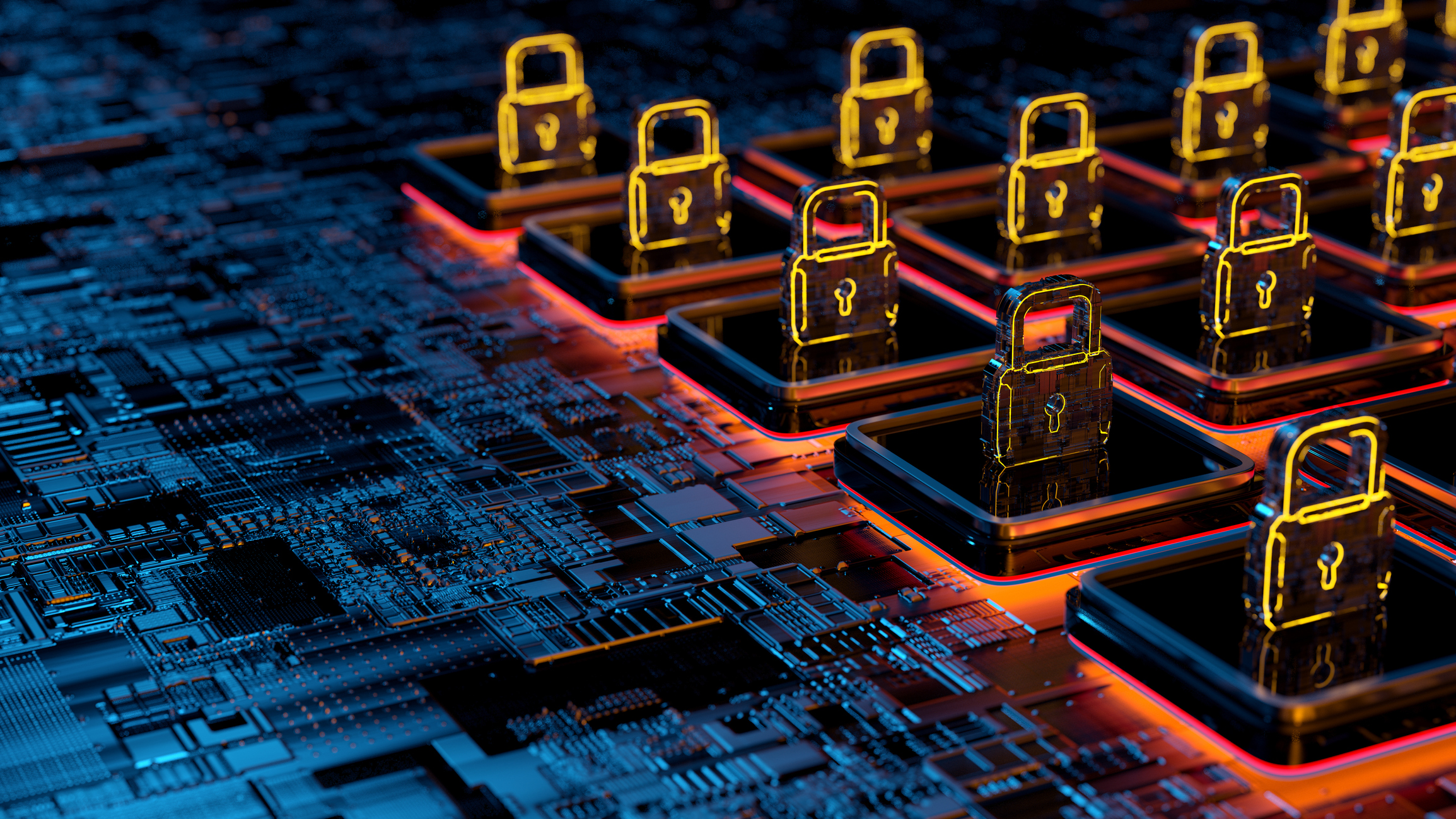
When most people think of someone hacking their business, they picture sophisticated cybercriminals infiltrating the network, breaking password protocols, and penetrating the firewall. Although that can happen, it’s very rare. Instead, social engineering is behind most cyberattacks, from high-profile data breaches at the largest corporations to ransomware and other attacks that many small and middle-market businesses (SMBs) fall victim to each year.
This kind of cyberattack doesn’t take a lot of money or sophisticated equipment to carry out, but the result can be quite costly for businesses. In 2020, data breaches cost companies on average almost $4 million per incident, according to the global IBM Security Cost of a Data Breach Report. Of the 17 industries surveyed, healthcare had the highest average total cost at $7.13 million.
Common Social Engineering Attack Vectors
Hackers can access a company’s sensitive information through a variety of social engineering techniques: faking the identity of an authorized user, guessing login credentials by mining social media profiles, or even boldly walking into the office and sitting down at an unsecured workstation. The three most common methods of trying a social engineering attack on an SMB are:
- Email — This indispensable business tool is valuable to would-be hackers, too. Many businesses are working harder to train staff to watch for potentially fraudulent emails, but it’s still an extremely successful attack vector — partly because it’s so easy to make an email appear to be coming from someone other than the true sender.
- Telephone — Phone calls are another common tactic. The caller pretends to have a legitimate request for access to systems or information, and if the recipient complies, cybercriminals can gain the data they seek.
- Physical access — In this tactic, hackers pretend to belong somewhere, such as a bank, an office, or a restricted-access area like a server room. If it works, they can get into the network using their own equipment or through an unattended workstation (even easier, since it’s probably already logged in). Once in, they’re free to steal, delete, or corrupt data as they like, or to install viruses and malware that infect the system.
Why Does Social Engineering Work?
Psychology is key to a successful social engineering attack. People don’t want to get in trouble, and they are curious by nature. For example, an email attachment claiming to offer tantalizing information — the salaries of everyone at the company, perhaps — is nearly irresistible. If the document carries malicious content like a virus or ransomware, just one click can put the entire network at risk.
Similarly, a bad actor posing as an IT auditor with an urgent request to test the safety of employee passwords is often successful; nobody wants to be the person who quibbles about protocol, holding up important work that makes the whole company safer. By exploiting either of these two basic human traits, hackers can bypass even the most sophisticated and carefully planned security systems.
Prevention Starts with Training and Testing
Individual behavior is what allows hackers in or keeps them out, so when it comes to thwarting social engineering attacks, training and testing are the two most effective prevention strategies.
Frontline workers need to understand how to recognize when something is out of the ordinary and how (and when) to report it. But while knowing what to look for can help people identify potentially risky situations, it’s also crucial that they know exactly how to respond.
Every business should have a written policy detailing protocols for verifying the identity of callers, email senders, and in-person visitors. For example, if an email contains any red flags at all, recipients should know to contact the IT department using a familiar number or help desk email address — not via a number or link included in the email — to verify that it’s legit (and do this before clicking on links, downloading attachments, or responding to the email).
It’s also critical that the training includes simulations and practice sessions. After all, it’s one thing to understand the policy in theory, and quite another to react appropriately when it’s happening. The goal is to impart a healthy skepticism in all members of the organization, so that they become comfortable and confident following established procedures in real-world scenarios.
Frequent white-hat social engineering testing is another imperative. This allows the company to identify vulnerabilities, whether that’s a particular attack vector (e.g., email requests or a sensitive location that needs more security) or specific individuals who need more training. Those who fail a test need to know that they failed and receive retraining and coaching, until it becomes automatic to follow established procedures before taking any action that could open the door for hackers.
In addition to training and testing, businesses can adopt tech-based strategies to help stop social engineering attacks. Companies that run their own mail server should implement some type of third-party protection tool that can scan incoming mail for viruses and malware. Some businesses go so far as to forbid attachments completely unless they go through a secure method of transfer, such as a file share platform that ensures the validity of each attachment. And for physical threats, camera systems can send an alert to those responsible for information security when someone enters an area with servers or other sensitive equipment.
The First and Last Line of Cybersecurity Defense
Tools like these can reduce risk, but don’t make the mistake of thinking they’ll provide adequate protection or make up for human error. Cybersecurity experts like to say that in social engineering, your people are your first and last line of defense. Training and testing (and retraining, if necessary) really are the keys to preventing a successful social engineering attack.
Cybercrime isn’t going away, but you can mitigate the risks of social engineering with effective training, testing, and tools. Contact the cybersecurity professionals at CRI for help keeping your business safe.