Whaling Cyberattacks: What You Need to Know
- Contributor
- Tim Gruters
Feb 2, 2016
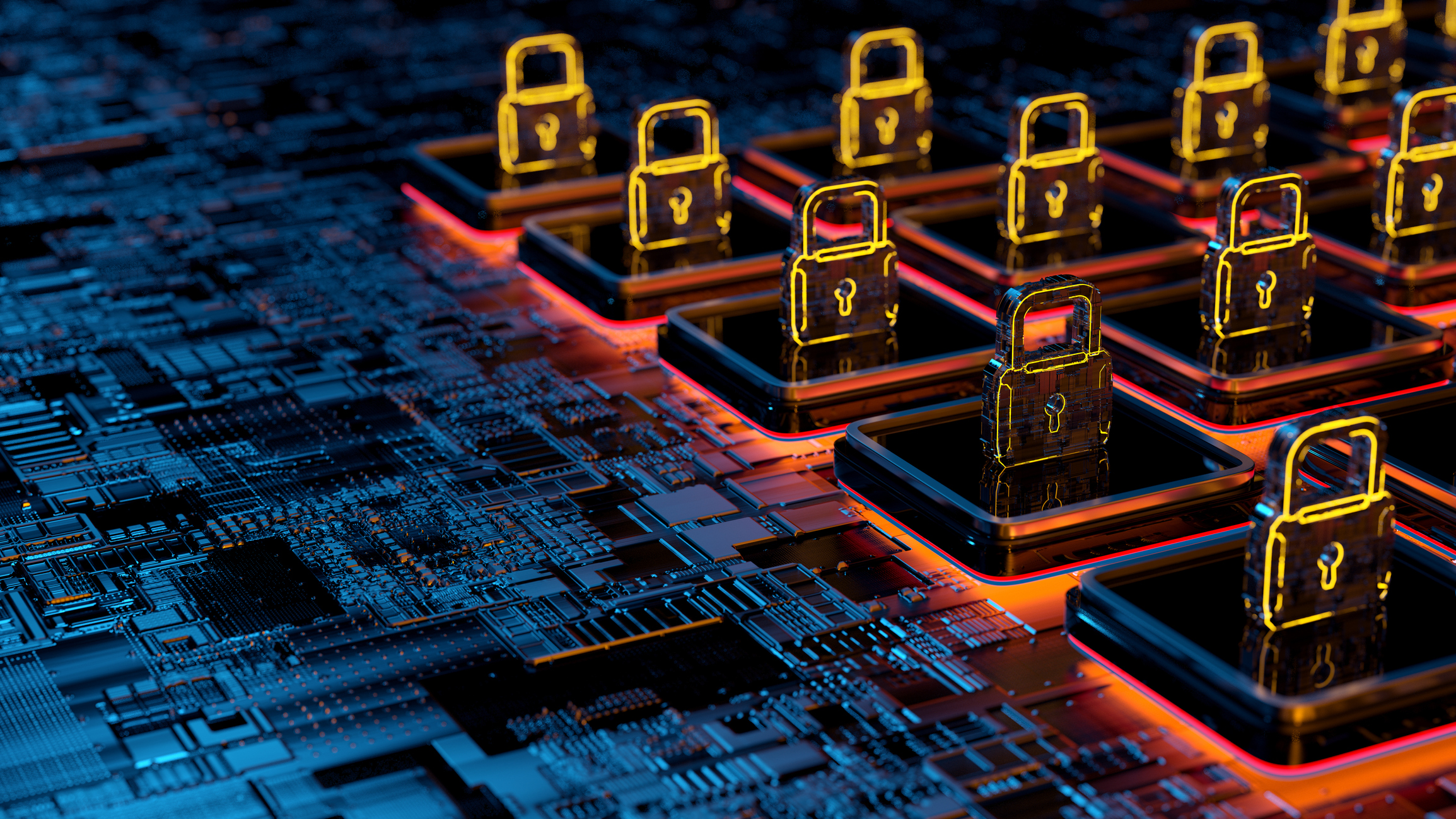
Cyberattacks are here to stay—partially because the financial result is lucrative for the criminal and partly because the bad guys can easily hide from law enforcement. It seems to have started with three common types (one of which that has morphed) and have taken off in the below order:
- phishing*, which includes blast emails designed to entice the reader to click on a bogus link or attachment,
- vishing, which is basically phishing utilizing phones to replace email as the vehicle, and
- pharming, which involves controlling personal computers via servers and/or routers.
*Recently, phishing has evolved to include spear phishing—an attack directed at a specific target versus indirectly to a group of people—and led to the latest (and perhaps “greatest,” if you will) of these threats: whaling.
What is a Whaling Cyberattack?
Simply put, a whaling cyberattack is closely related to spear phishing, but the target is a much bigger “phish.” Specifically, a whaling attack is directed at senior management and other executives. Whaling targets those key individuals in a way so that the fraudulent communications that are sent appear to have come from someone within the organization, typically a senior leader or influential individual such as a CEO or CFO. This adds an extra element of social engineering, with staff reluctant to refuse a request from someone they deem to be important.
This “targeted” information is sometimes, if not often, available on an entity’s website. Additionally, some cybersecurity experts believe that this type of information is also being sold on the black market.
Whaling cyberattacks also differ from phishing because the goal is bigger than stealing a victim’s identity. These cybercriminals are harpooning for control of the executive’s personal computer to determine passwords and gain access to critical digital assets, information, and confidential information.
How Is the Whaling Net Cast?
Often the whaling email is related to “official” business, such as a subpoena supposedly being issued against the executive or a complaint filed with the Better Business Bureau. The email often uses icons and language that seem official, and it usually conveys a sense of urgency (e.g., a threat for non-responsiveness). In reality, hidden underneath the blubber of an attached “subpoena” document or the necessary software download are malware (usually a Trojan/keylogger)—or the email includes a hyperlink directing the victim to an infected website.
Don’t Let Your Employees Become Victims of a Whaling Cyberattack
This new threat has been quite successful to date and isn't worth falling victim to if you can help it. Contact your local CRI professional to engage our cybersecurity professionals for help building an education and training program that better protects your business from whaling attacks.